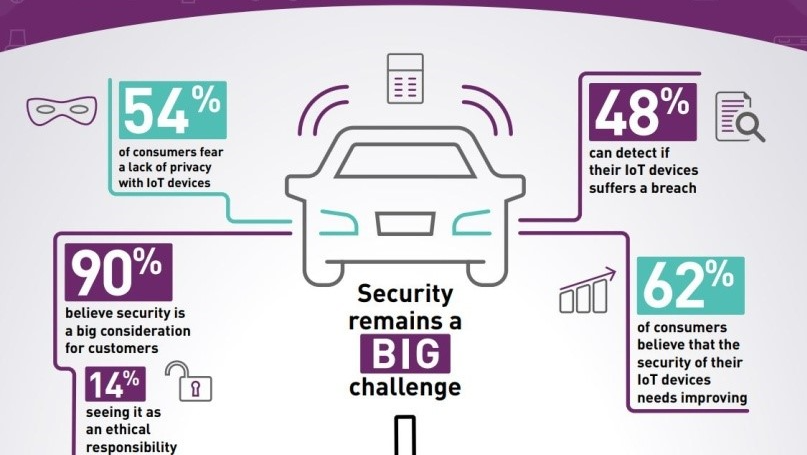
Do you trust Security & Privacy in IoT?
According to Market Research, the global IoT Security Market size will grow from USD 14.9 billion in 2021 to USD 40.3 billion by 2026!
A survey shows 55 percent of IT professionals list IoT security as their top priority!
What is the hint in this data point? What it implies?
To answer the question above let us first look at what is IoT and the industries that use IoT. The Internet of Things (IoT) is a system of Interrelated, Internet-connected physical objects. These objects, collect and Transfer Data over a Wireless Network without Human Intervention. To know more about IoT read our blog at: https://www.starcertification.org/blog/is-there-a-future-scope-of-iot-in-modern-world/
The industries that lead the IoT revolutions are as follows:
Transportation, Manufacturing, Utilities, Healthcare, Consumer electronics, Driverless cars, Logistics, Oil and Gas, Mining, Aviation, and so on… The benefits of using IoT are – Connected factories, Production visibility, Inventory management, Safer work environment, Secured facilities, Predictive maintenance, Predictive forecasting, Reduced carbon footprint, Improved quality, and Increased operational Efficiency.
All of these advancements provide with an opportunity to cybercriminals. They can exploit numerous points within an IoT ecosystem. It can be sensors, software, network, and storage. Does it mean that you stop using your connected devices? Absolutely not. You should look for applying security to every end point.
It’s a digital world today. This increases incidents of IoT Security lapses. Will mention a few security lapses here. Not to scare you but to look at it critically so that you may learn from it.
Bitdefender’s security researchers discovered and reported a flaw in Amazon’s Ring Video Doorbell Pro. Hackers could have exploited this to gain access to the user’s Wi-Fi network and other connected devices on it. Amazon rolled out patches for the vulnerabilities and urged its users to update their devices to improve the issue.
FBI has raised a security issue that states, smart TVs have several ignored security issues. Hackers can not only access your remote control, but also can track your everyday conversations by using the integrated microphone.
Hackers can compromise infrared-enabled smart bulbs by sending commands via an infrared invisible light emitted from the bulbs to exploit other IoT devices connected to the Wi-Fi.
Academic researchers from England and Sweden designed a malware that can exploit a smartphone’s microphone to steal the device’s passwords and codes by hearing your touch, a new Acoustic Side-Channel on Smartphones.
According to Vince Steckler, a chief executive of Avast, smart coffee machines can allow owners to control them remotely using their phones. Users can even give the machines vocal commands if they are connected to virtual assistant software such as Amazon’s Alexa.
A report highlighted that 60 percent of businesses in the U.K., U.S., France, and Germany suffered a print-related data breach last year. This resulted in a data loss. It cost companies an average of US$ 400,000+
Researchers at Trend Micro discovered that hackers are targeting internet-connected gas stations to launch IoT-based cyberattacks.
What Should You Know About IoT Security?
With expected, 75 billion IoT devices worldwide by 2025, 73 Zettabytes of data collected from IoT devices by 2025 and the global IoT market size of USD 1,386.06 billion by 2026, the connected devices can give businesses a real boost. A word of caution here – anything that’s connected to the Internet can be vulnerable to cyberattacks.
Do you know the IoT Opportunities and Risks:
| IoT Opportunities | IoT Risks |
| Improved asset utilization | Cybercrime, cyberwar and cyberterrorism |
| Real-time optimization | Data and Privacy breaches |
| Greater end-user insight | Botnet, ransomware and malwares |
| Enhanced decision making | DDoS attacks and other sabotages |
| Easier access to information and services | Product malfunction through remote control |
IoT security provides blanket protection to networks, systems, devices, and data from a host of IoT security attacks. It is the segment of technology that keeps the IoT systems safe by safeguarding connected devices and networks. The IoT Security protects devices from vulnerabilities, threats and breaches. It identifies, monitors and fixes vulnerabilities. It ensures the availability, integrity, and confidentiality of IoT solution.
What are the types of IoT Security attacks? Everything that is connected to the IoT environment is susceptible to security attacks. A smart home, an IoT connected car, a manufacturing unit, a smart power grid – every industry that uses IoT devices is exposed to IoT security threats with varying severity of the impact.
Broadly, there are 4 types of security attacks – Lifecycle, Communication, Software and Chips. Lifecycle attacks happen when the IoT devices change hands from user to maintenance. When data is transmitted between IoT devices and servers, communication attacks can take place. The connected devices have in-built software that can be attacked. Physical attacks that directly target the device chip.
Are you aware of the IoT Security challenges? There are plentiful challenges that prevent end-to-end implementation of IoT security solutions today. Infected devices may run normally and still compromise information uninterruptedly. Hackers keep looking for these devices to gather information. The compromised device stays invisible and outflows information in small packages. Once the sufficient information is collected, the hacker may open a major attack. The IoT devices are resource-constrained. They do not have the chips that can compute data received from various sensors. They are not designed to run with advanced security features. Let’s highlight few other IoT security challenges:
- User Authentication System: Setting a proper user authentication system has always been the biggest challenges. The IoT networks have quite a lot of devices and their different authorization needs make it difficult to set proper user authentication systems.
- Complex Network: It is difficult to pinpoint the weak points of a complex network of devices that keep adding devices. Any additional device in the system brings new vulnerabilities that hackers may exploit if left unprotected. To understand the complexity, let’s assume that a device within the IoT network has run a compromised program. The hackers may access sensitive information by getting access to this device. Being a complex network it will be difficult to pinpoint a compromised device and more the time it takes higher the risks involved.
- Software Updates: Did you update your software in last 6 months? An outdated software is an easy prey of the hackers. The software updates are released to protect from the latest malwares. Software companies release updates because there are changes in the application structure. If it is not updated in time it can be an open invitation to the hackers.
- The Legacy Assets: Do you know that companies avoid buying new devices or software? They try to add a legacy asset, a software or hardware? Why? To avoid the huge expense associated with it. These legacy assets are connected to the IoT network without much of changes. This calls for a cyberattack. Remember that the after attack expenses are far more than replacing the old-dated devices.
- Pressure of Introducing a New Product: How many new IoT devices or applications you came across in last 3-6 months? There is a competition in the market to release an IoT product before the other company does. Their focus is on launching the product in the market at the earliest even if the security is compromised. Products without a security check from its inception, are exposed to cybersecurity threats.
- Human Error: Be it an organization or a home, human error is one of the major concerns for IoT security. User may accidentally click on insecure links, access unsafe websites, or use a public Wi-Fi connection on IoT devices. These activities leave a trail on the internet and following these trails the hacker enters the IoT network. More the employees more the merry for hackers. Monitoring employee activity is challenging, and human errors are inevitable. Lost sight and the accident happened! To know more about human errors read our blog at: https://www.starcertification.org/blog/cybersecurity-awareness-month-week-4-cybersecurity-first/
What are the levels of IoT Security? What do you think? You now know that there are many ways that can damage the IoT Network. It needs a comprehensive set of shields. 5 Levels of IoT Security implementation need to be added. They are as follows:
- User Interface
- Operating System
- Firmware
- Hardware
- IoT Chip.
For example, the user interface needs to trust the Operating System. The operating system in turn needs to trust the firmware, and the firmware needs to trust the hardware circuits operating in the IoT Chip layer. This creates a hierarchy for security and the need for a strong foundation on which to build.
How do we secure the complex IoT Network? A secure network enhances IoT device security exponentially. The measures that could be taken are:
- Securing ports by opening them when it is required.
- Using anti-malware and firewalls.
- Deploying Intrusion Detection or Prevention Systems (IDS or IPS).
- Blocking unauthorized IP addresses.
- Patching and updating all systems
- Implementing Security Gateways

How an individual and an Industry can play their roles in IoT Security? The smartphone usage statistics suggest that an average person spends 2 hours and 51 minutes per day on their mobile device. 22% of users check their phones every few minutes, and 51% of users look at it a few times per hour. What is the catch in this data? “Keep a tab on smartphones” and follow the rules:
From an individual’s point of view:
- Make sure to log-in to and log-out of the devices.
- Use a strong password or biometric options so that you can avoid data loss .
- Segregate personal and business data and activate data wipe feature on devices to wipe the stolen data.
- Use reliable security products that will restrict harmful apps to run on the devices.
- Set up automatic antivirus updates to protect devices from a cyberattack.
- Always change the default password on new devices.
- Never re-use the same password across devices.
From the point of industries:
- Restrict internet usage through connected devices to prevent critical data leak.
- Password protection should be compulsory to allow access to any software.
- Buy the products after a thorough research and from a reputed cybersecurity company.
- Set up end-to-end encryption for the connected devices.
- Firewalls should
- Make sure the device and software updates are available and installed.
- Implement automatic updates as per the business requirement scenario.
- The identified lapses must be immediately resolved by performing periodic security inspection.
- Keep track of available features of a device and disable the unused features.
- Disable the connected devices that are of temporary use.
- Make tamper-proof devices through hardened security.
- Staff Training.
- Educate Consumers.

Many a times the security teams struggle with IoT and operational system security. Why? It is because the concepts are still new for them. Industries must keep training the staff and keep them updated for unknown security challenges. Trainings will make the teams to stay up to date with modern cybersecurity threats and implement protective or preventive measures as the requirement be.
The Star IoT Security Specialist (SISS) by Star Certification, is the most advanced certification in the information security domain. This certification focuses on securing the Internet of Things (IoT) devices. The SISS certification provides the knowledge of IoT architecture, attacks, threats and risks, penetration testing and securing connected devices. The course starts with the key concepts of IoT and its security, and then moves towards the concepts required to perform the penetration testing on IoT devices.
Star Certification, an international certification is a Vendor-Neutral and Open-Source IoT Certification Body, Star Certification has courses in IoT, IoT Security, Cybersecurity, Disruptive Technologies, and Software programming with International certification.